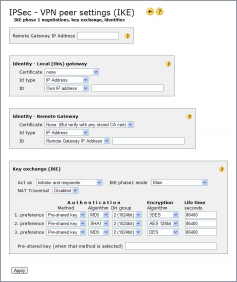
VPN Peer Settings
After clicking “Add peer” the “VPN peer settings” page appears. These are the configurations describing the remote IPSec gateway you want to connect to and how the IKE negotiation with it should be performed.
Many of the fields are pre-configured to suit most common IPSec applications. Some other fields are empty and must be filled in by you before Apply-ing the page:
Remote Gateway IP Address – here you must enter the global IP address the IPSec gateway you want to access can be reached at. The address must be a static IP address. (A DNS name is not supported).
Pre-shared key – here you must enter the pre-shared key to be used for authentication. Pre-shared key
If you are using certificate for authentication then change authentication method in all three preferences, and select the certificates used in the Identity fields.
To create an EasyServer peer entry specify “0.0.0.0” as “Remote Gateway IP Address” and “Act as: Responder for roaming clients”. Enter pre-shared key or certificates as described above.
Other VPN peer settings fields
The above-mentioned fields are the ones you MUST specify. Other fields are pre-configured to suit most common IPSec applications, but you might need to change them to suit your needs. A rule of thumb is that both ends of an IPSec connection must use the same configuration to be able to connect.
Identity – Local (this) gateway
These settings control how your Internet Gate identifies itself to the remote gateway. The values in these fields must match the identity preferences of the remote gateway.
Certificate If certificates shall be used for identification, select the one to be used from the list of available own certificates.
Id type This unit can identify itself either by its IP Address or by some field of its certificate: Domain name, E-mail (user DN), or ASN.1 Dist. name.
The selected ID type must correspond to what the remote peer expects to see. ASN.1 Distinguished name is the most common when using certificates, IP address when using pre-shared key.
ID:
- If Id type: IP Address is selected then select either Own IP address for your unit's own global IP address, or Other, specify and enter IP address manually into the field.
- If Id type: ASN.1 Dist. name is selected then select either Use ASN.1 in cert to use the ASN.1 field in the certificate selected above, or Other, specify and enter the distinguished name manually into the field. ASN.1
- If Id type: Domain name or Id type: E-mail (user DN) is selected then select Other, specify and enter it manually into the field.
Identity – Remote Gateway
These settings control how your Internet Gate verifies that it has connected to the correct remote gateway. The values in these fields must match the way the remote gateway identifies itself.
The most common identification type for connections with pre-shared keys is IP Address. The ID: Remote Gateway IP Address configuration makes your Internet Gate compare the remote gateway's IP address with the one you have specified in the Remote Gateway IP Address field at the top of the page.
The most common identification type for connections with certificates is ASN.1 Dist name. ASN.1
You can turn off remote gateway identification verification by selecting ID: Any ID (no ID check). Then your Internet Gate will accept any remote gateway regardless of how it has identified itself.
Certificate If certificates shall be used for identification, select the one to be used from the list of available trusted certificates.
Id type The way the remote peer is expected to identify itself: either by its IP Address or by some field of its certificate: Domain name, E-mail (user DN), or ASN.1 Dist. name.
ID:
- If Id type: IP Address is selected then select either Remote gateway address for the remote peer's global IP address, or Other, specify and enter IP address manually into the field.
- If Id type: ASN.1 Dist. name is selected then select either Use ASN.1 in cert to use the ASN.1 field in the certificate selected above, or Other, specify and enter the distinguished name manually into the field. ASN.1
- If Id type: Domain name or Id type: E-mail (user DN) is selected then select Other, specify and enter it manually into the field.
- To bypass ID checking (all ID-s are accepted) select Any ID (no ID check).
Key exchange (IKE)
These settings control the IKE (Internet Key Exchange) negotiations between your and the remote IPSec gateway. IKE
Act as:
By default your Internet Gate acts as both IPSec Initiator and responder, meaning it can initialize an IPSec connection when needed, but also answer to an incoming connection request from the specified remote IPSec gateway. You can change it to just responder: then your Internet Gate becomes more like a “server” only accepting access from the specified “client”, but not trying to connect to it by itself. The Responder for roaming clients setting is for the EasyServer.
- Initiator and responder: this unit accepts connection attempts from the remote peer, and also tries to initiate connection by itself if there is any data to be sent to the remote peer. ( “client” )
- Responder: this unit accepts connection attempts from the remote peer, but does not attempt to connect to the remote peer by itself. (“server”)
- Responder for roaming clients: this unit accepts connection attempts from unspecified remote peers. Remote Gateway IP Address (see above) does not need to be specified - set it to 0.0.0.0
IKE phase1 mode
During the initial security association establishment, one can select between:
- Main: a little more secure and requires two more message exchanges,
- Aggressive: a little less secure but faster, the identities are not protected,
- Main, accept Aggressive: Main mode preferred, Aggressive mode accepted,
- Aggressive, accept Main: Aggressive mode preferred, Main mode accepted.
NAT Traversal
Specifies whether IPSec NAT-T protocol (encapsulation of IPSec packets inside UDP packets) is allowed to be used when your Internet Gate acts as an Initiator. It is useful if you, or the remote IPSec gateway, are behind a NAT. As an IPSec responder the Internet Gate always accepts IPSec NAT-T packets. NAT-T
- Disabled: NAT-T will not be used, connections with a NAT (=Network Address Translation) in between will not work.
- Enabled: NAT-T will be used if needed (and if supported by the remote peer), automatic detection if a NAT is present is done.
- Force: If the remote peer supports NAT-T, then it will be used, even if no NAT is present. This is e.g. useful if the ESP- or AH-protocol is blocked somewhere on the communication path.
List of algorithm offers
At least one of the preferences listed must be exactly like the remote IPSec gateway's preferences. The default preferences are chosen to be compatible with most IPSec applications, but in some circumstances you might need to alter them to fit the remote IPSec peer's.
Authentication:
- Method RSA or DSS signatures are used with certificates, pre-shared key otherwise. RSA is considered to be safer than DSS. Digital signature Pre-shared key
- DH group The Diffie-Hellman group to be used for this preference. The choices are listed in increasing security but decreasing performance order. Diffie-Hellman
Encryption Algorithm Algorithm used to encrypt the exchange of the randomly generated encryption keys to be used in the connections for data-traffic. The choices are listed in increasing security but decreasing performance order. DES 3DES AES
Life time A new IKE key exchange is performed after the specified time (in seconds) has passed.
Pre-shared key - if Pre-shared key was selected as Authentication Method: 8-40 preferably random characters, not known by anyone else but you and the remote gateway.